Your iPhone’s encryption means nothing when 100 governments now wield commercial spyware that bypasses every security measure you trust. UK intelligence reveals this staggering jump from 80 countries in 2023, transforming nation-state hacking from an abstract threat into a personal phone security crisis.
The Spyware Reality Check
Tools like Pegasus infiltrate devices through “zero-click” attacks that require no user interaction.
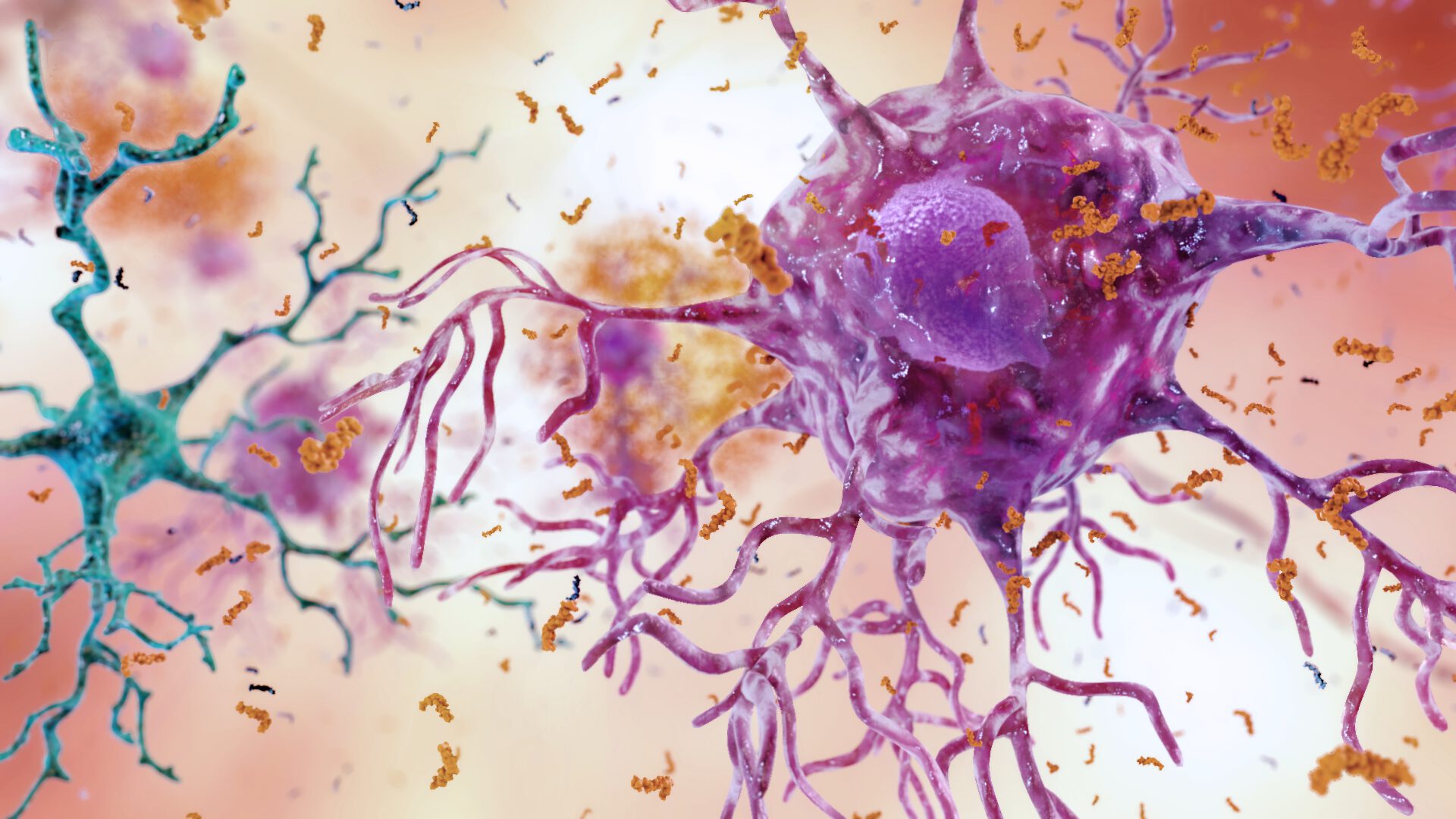
Commercial spyware operates like digital lockpicks for your most personal device. NSO Group’s Pegasus and Paragon’s Graphite exploit security flaws in phone software to steal everything—messages, photos, location data. The leaked DarkSword toolkit demonstrates how these nation-state tools reach cybercriminals, enabling attacks on unpatched iPhones and iPads through malicious websites you might visit unknowingly.
These aren’t theoretical vulnerabilities. They’re weaponized exploits deployed against real targets who thought their devices were secure.
Beyond Criminals and Terrorists
Bankers and business professionals now face the same surveillance risks as journalists and activists.
The target list has expanded dramatically beyond traditional espionage victims. If you handle sensitive business data, manage financial transactions, or work in sectors that governments find strategically interesting, you’re potentially in scope.
Richard Horne, head of the UK’s National Cyber Security Centre, warned that British companies are “failing to grasp the reality of today’s world” regarding these modern threats.
This shift reflects how commercial spyware has democratized sophisticated surveillance capabilities, making once-exclusive intelligence tools accessible to governments lacking indigenous cyber capabilities.
The Proliferation Problem
Affordability and leaks put military-grade hacking tools in more hands than ever.
The mathematics of this threat are sobering. When specialized surveillance technology becomes commercially available, it inevitably spreads through corruption, leaks, and secondary markets. Non-state actors—including criminal cartels—now access these tools through compromised government contracts or insider theft.
China-linked intrusions targeting data theft represent just one facet of this expanding threat landscape, with pre-positioned attacks designed for potential future conflicts adding another layer of risk to everyday device usage.
Your smartphone‘s privacy settings suddenly seem quaint when weighed against tools designed to circumvent every consumer protection. The international community scrambles toward export controls and coordination, but the digital horses have already left the stable.