What if your enterprise network went dark during a crisis, but not from external attacks. Iranian state media claims exactly this happened to Cisco, Juniper, Fortinet, and MikroTik equipment during US airstrikes on Isfahan Province, alleging pre-installed backdoors triggered simultaneous reboots despite Iran’s total internet blackout.
The Backdoor Allegations
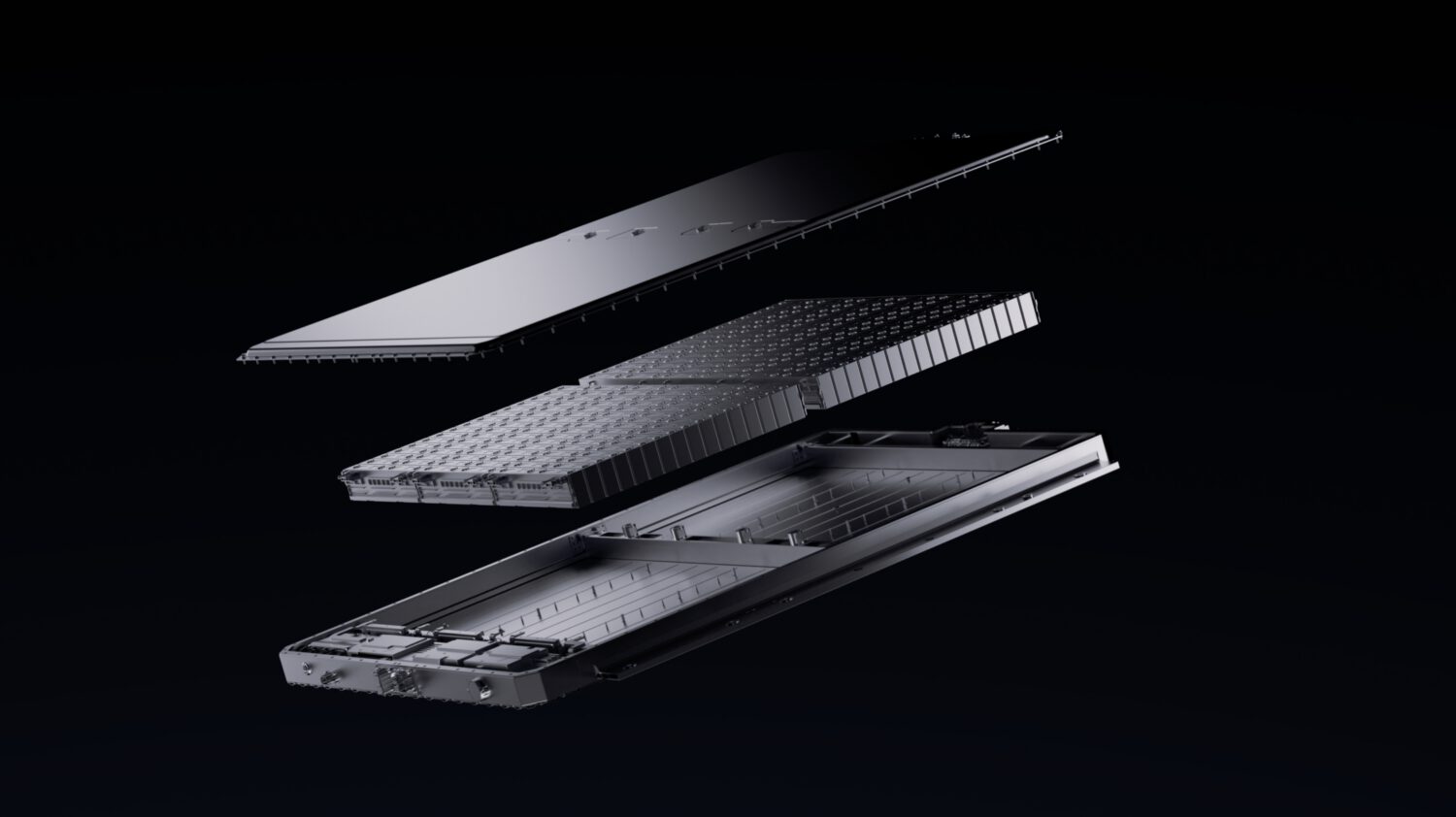
According to Iranian reports, routers and switches from major US vendors experienced coordinated shutdowns during recent conflicts, suggesting remote activation via satellite signals or firmware sabotage. Iran’s cyber labs promise technical evidence but haven’t released any proof as of April 2026.
The timing feels convenient—these claims emerged just as tensions escalated, though references to specific military operations remain unverified through official channels.
Technical Reality Check
Forum discussions reveal more plausible scenarios than Hollywood-style backdoors. Network engineers suggest:
- Pre-disconnection commands
- Malicious packets exploiting unknown vulnerabilities
- Basic misunderstanding of how internet speed isolation works
Cybersecurity analysts note that internal malicious packets triggering zero-day vulnerabilities offer a more straightforward explanation. Your average enterprise router handles thousands of packets daily—finding exploitable flaws doesn’t require manufacturer complicity.
The Verification Problem
Here’s the catch: NetBlocks has documented Iran’s strict internet segregation, with selective access only for favored groups and officials with special access credentials. Independent security researchers can’t verify these claims because Iran controls all digital evidence.
This creates perfect conditions for propaganda—making allegations while preventing outside investigation, highlighting broader computer problems in enterprise environments.
China Amplifies the Message
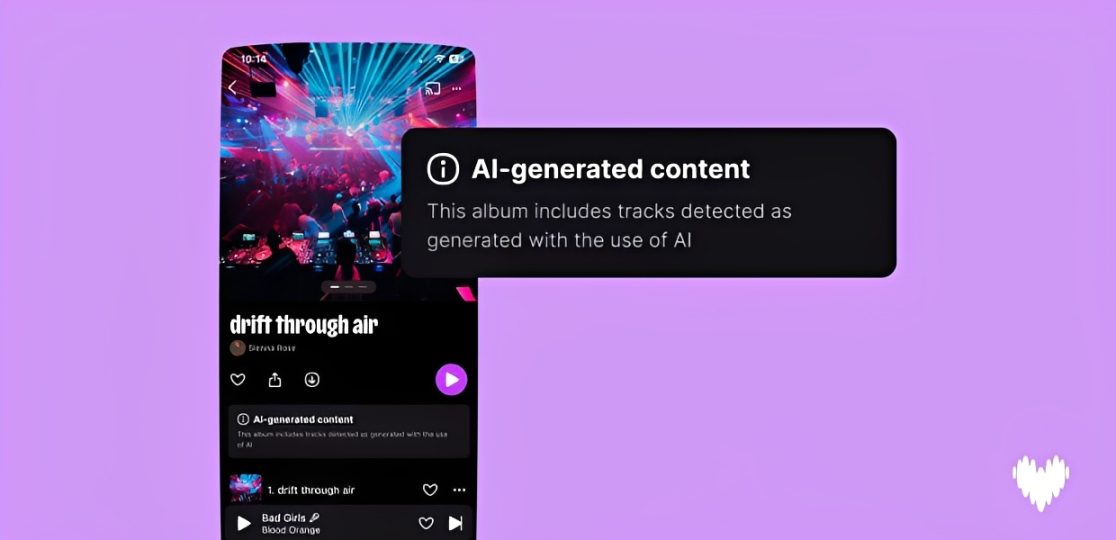
Chinese state media reportedly republished Iranian reports, complete with hardware-focused imagery. This isn’t coincidence—it’s strategic messaging. By highlighting alleged US backdoors, China deflects accusations about operations like the documented Volt Typhoon APT group while positioning Beijing as the cyber-pacifist.
The Snowden revelations provide historical context for surveillance capabilities, but that doesn’t validate these specific claims. These sophisticated criminal networks demonstrate how state-level cyber operations continue evolving.
Your enterprise networking decisions just got more complicated. Whether these allegations prove true or false, they highlight genuine supply chain vulnerabilities that deserve serious attention beyond geopolitical theater.