When you’re choosing the best router for your needs, consider critical factors like Wi-Fi speed, range, ease of use, and signal reliability. For instance, routers should offer solid performance on both the 2.4 GHz and 5 GHz bands, providing ample speed for streaming and gaming. It’s also essential to prioritize features like QoS for bandwidth management and MU-MIMO support for multiple device connections. Ensuring good firmware and easy setup can significantly enhance your experience, avoiding common issues like connection drops and poor range.
Our guide features four top-performing routers selected from a rigorous analysis of 37 models and over 191,622 reviews. We used our proprietary True Score system, certifying these products as tested, and filtered out fake reviews, with 49% of so-called expert opinions failing our Trust Rating criteria. The winning routers demonstrated reliable performance, ease of use, and excellent connectivity, standing out as the best options available.
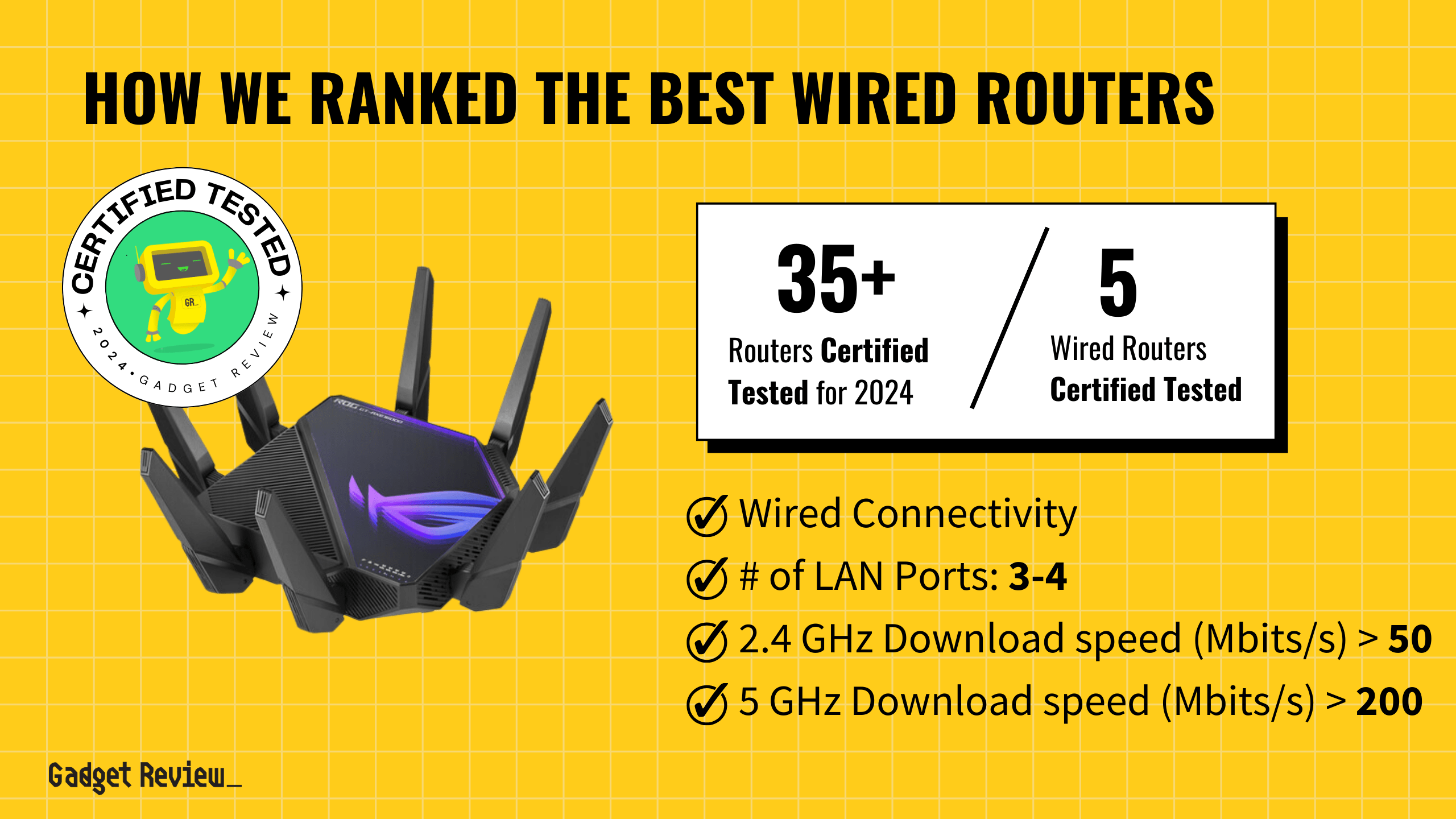
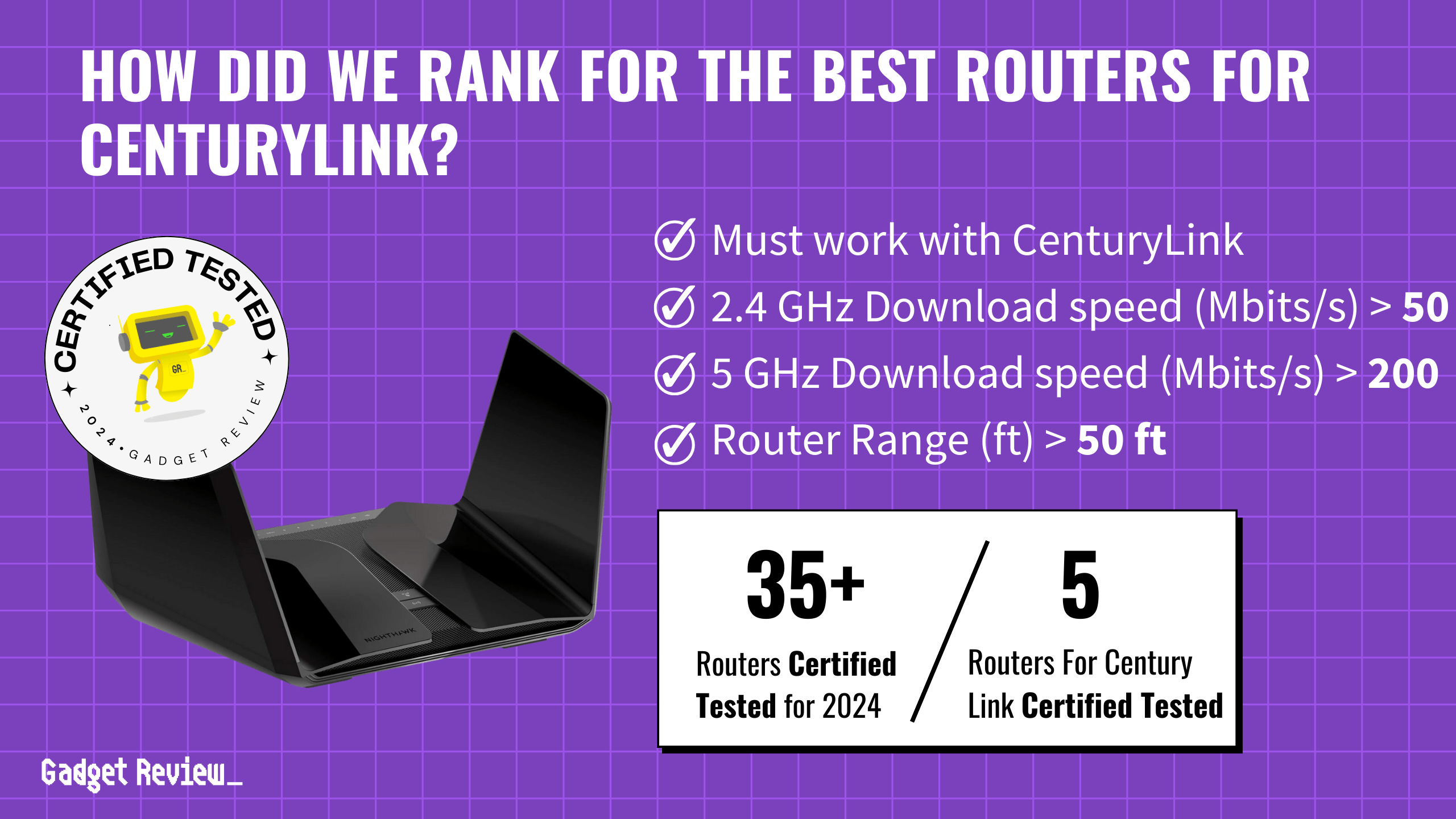
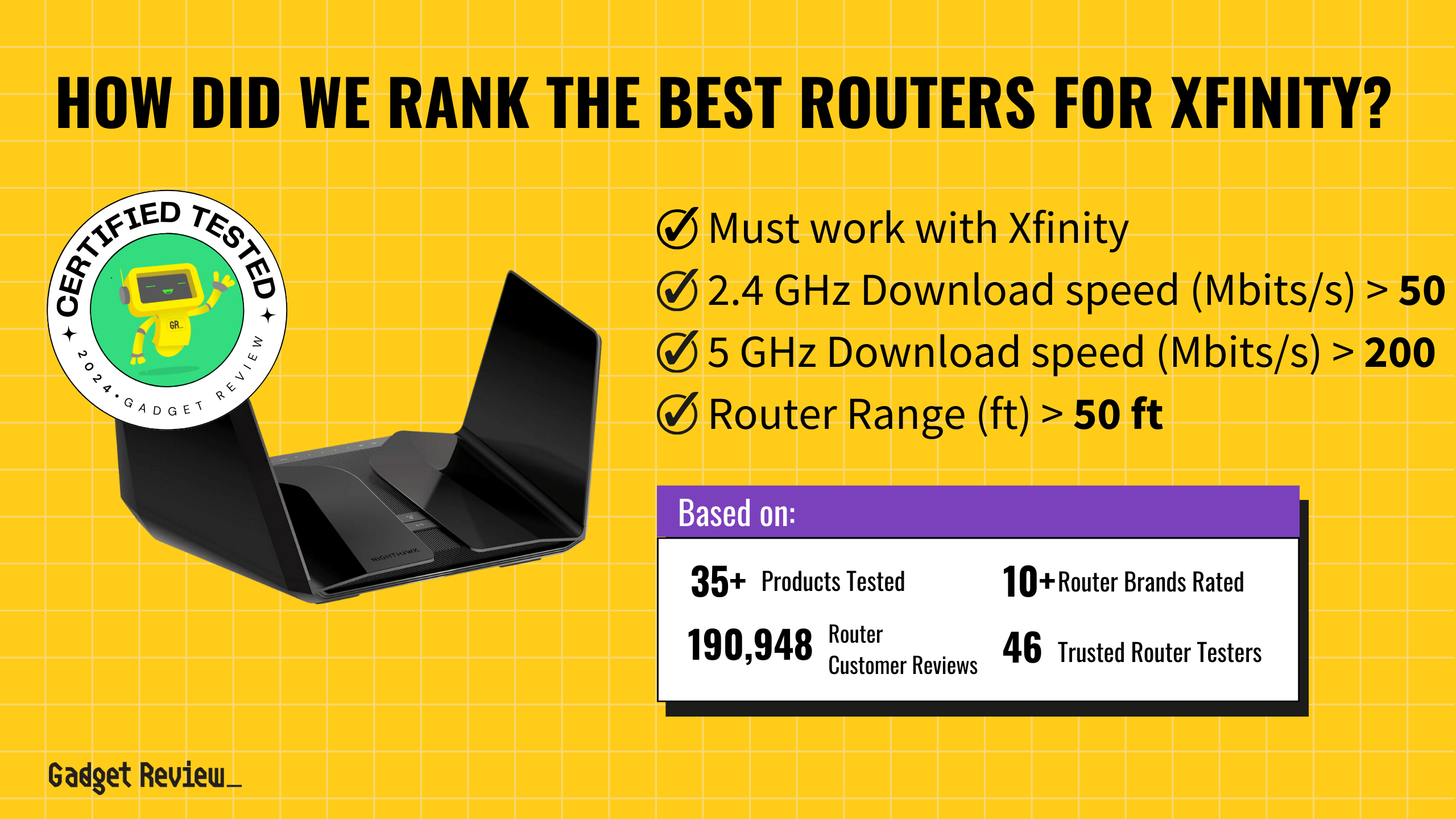
How Did We Rank the Best Routers?
The best routers are capable of delivering consistent speeds, good range, and low latency. However, the criteria we use to define what gets onto this list come with a big caveat: we know not every router can truly do it all. Some routers aren’t tri-band, and other routers don’t offer mesh network compatibility. However, every router on this list fulfills at least a few of these criteria, if not most of them, and comes with enough features to make them excellent in just about any home and in any budget.
| CRITERIA | RANGE | REQUIRED | DEFINITION |
|---|---|---|---|
| 2.4 GHz Download Speed | > 50 Mbits/s | Yes | The maximum speed that the router can reach when downloading on the 2.4 GHz band. |
| 2.4 GHz Upload Speed | > 25 Mbits/s | No (Nice to have) | The maximum speed that the router can reach when uploading on the 2.4 GHz band. |
| 5 GHz Download Speed | > 200 Mbits/s | Yes | The maximum speed that the router can reach when downloading on the 5 GHz band. |
| 5 GHz Upload Speed | > 100 Mbits/s | No (Nice to have) | The maximum speed that the router can reach when uploading on the 5 Ghz band. |
| 6 GHz Download Speed | > 250 Mbits/s | No (Nice to have) | The maximum speed that the router can reach when downloading on the 6 Ghz band. |
| 6 GHz Upload Speed | > 125 Mbits/s | No (Nice to have) | The maximum speed that the router can reach when uploading on the 6 Ghz band. |
| Router Range | > 50 ft | No (Nice to have) | How far a device can be from a router before the signal starts degrading. It is worth noting that 2.4 GHz reaches further than 5 GHz. |
| Latency | < 40 ms | No (Nice to have) | The delay that is created by a signal being sent by the router and then received. |
When you shop through our links, you’re backing our mission. Dive deeper to see how.
Latest Updates
- 08/12/2024: Republished the list to include the best routers based on our True Score system.
Top Routers For 2025
Prices accurate at the time of publishing

Best Overall

Runner Up

Best Value

Best Budget

Best Mid-Range

Premium Pick
Netgear Nighthawk RAXE300
Best For Best Overall
The Netgear Nighthawk RAXE300 is an excellent high-performance router for fiber optic internet, offering top-tier speeds, low latency, and wide coverage for gaming, streaming, and home offices.

True Score
83829Experts
904kCustomers
Absolutely Fresh
 SAVE $62$219.99$158.40
SAVE $62$219.99$158.40Read More
Snapshot
Reasons to Buy
- Superb Wi-Fi speeds
- Wide range
- Simple setup
Reasons to Avoid
- Limited range (6GHz)
- No USB A port
- Subscription-based security solutions
Specifications

# of LAN Ports 6 
Frequency Bands 2.4 GHz, 5.0 GHz, 6.0 GHz 
MU-MIMO Support Yes 
Wireless Standard AC, AX, N 
Mesh System No 
Quality of Service Prioritization No 
# of Phone Ports 1 
# of WAN Ports 1 
App Compatible Yes 
Available Storage 256MB 
Band Technology Tri 
Data Encryption Type WPA-PSK, WPA2-PSK, WPA3 
Energy Star Certified No 
Integrated Modem No 
LAN Port Speed 4 Gb Ethernet 
Number of Antennas 6 
Parental Controls Yes 
Processor Cores Quad 
Processor Speed 1.7GHz 
WiFi Range 2500 sq.ft 
WiFi Speed 7.8 Gb 
Wired Speed 1000 Mb All Specs
Test Results
2.4 GHz Download speed (Mbits/s) 222 5 GHz Download speed (Mbits/s) 852 6 Ghz Download speed (Mbits/s) 757 Latency (ms) 5 Router Range (ft) 170 2.4 GHz Upload speed (Mbits/s) 0 All Retailers
- $158.40$220Save $62
Availability
In StockFree Shipping
Yes - $164.99$300Save $135
Availability
Free Shipping
No - $299.00$399Save $100
Availability
In StockFree Shipping
No - $299.99
Availability
In StockFree Shipping
Our Verdict
If you need a high-performance router that can handle fiber optic internet and cover a large area, the Netgear Nighthawk RAXE300 is an excellent choice. It boasts top-tier speeds with download rates of 221.65 Mbits/s on the 2.4 GHz band, 851.6 Mbits/s on the 5 GHz band, and 756.8 Mbits/s on the 6 GHz band. This makes it perfect for heavy-duty tasks such as competitive gaming, 4K streaming, and immersive VR experiences. The router also offers impressive upload speeds of 175 Mbits/s on the 5 GHz band and 247.2 Mbits/s on the 6 GHz band, ensuring quick and reliable data transfers, ideal for high-definition video calls and cloud computing.
The Nighthawk RAXE300 excels in providing a minimal latency of just 5 ms and a broad range of 170 ft, making it a reliable option for gamers who need precision and for large homes that require consistent coverage. Its advanced security features and support for the latest wireless standards make it a forward-thinking investment, future-proofing your home network.
Overall, the Nighthawk RAXE300 offers superior download and upload capabilities, low latency, and wide-reaching coverage, making it a standout router for gamers, streamers, home offices, and small businesses. While it may not be the absolute fastest in every category, its robust performance and ability to handle multiple high-bandwidth activities simultaneously make it a great value for maximizing your fiber optic internet service.
Read Less

Best Overall

Runner Up

Best Value

Best Budget

Best Mid-Range

Premium Pick
Asus RT-AX86S
Best For Gaming
The Asus RT-AX86S is an exceptional budget-friendly gaming router, offering impressive speeds, broad coverage, and advanced features, making it ideal for gaming, streaming, and everyday use.

True Score
83823Experts
891kCustomers
Absolutely Fresh
 $132.96
$132.96Read More
Snapshot
Reasons to Buy
- Fast WiFi and download speeds
- Incredible range of coverage
- Easy installation and set up
- Low Latency
Reasons to Avoid
- Lacks Backhaul and Mesh Networking
Specifications

# of LAN Ports 4 
Frequency Bands 2.4 GHz, 5.0 GHz 
MU-MIMO Support Yes 
Wireless Standard AC, AX, N 
Mesh System No 
Quality of Service Prioritization Yes 
# of Phone Ports n/a 
# of WAN Ports 1 
App Compatible Yes 
Available Storage 256MB 
Band Technology Dual 
Data Encryption Type WPA, WPA-Enterprise, WPA2, WPA2-Enterprise, WPA3, WPA3-Enterprise, WPS 
Energy Star Certified No 
Integrated Modem No 
LAN Port Speed 4 Gb Ethernet 
Number of Antennas 4 
Parental Controls Yes 
Processor Cores Dual 
Processor Speed 1.8GHz 
WiFi Range 5400 sq. ft 
WiFi Speed 5.7 Gb 
Wired Speed – All Specs
Test Results
2.4 GHz Download speed (Mbits/s) 89 5 GHz Download speed (Mbits/s) 563 6 Ghz Download speed (Mbits/s) 0 Latency (ms) 15 Router Range (ft) 140 2.4 GHz Upload speed (Mbits/s) 0 All Retailers
- $132.96
Availability
In StockFree Shipping
Yes - $202.24$225Save $23
Availability
In StockFree Shipping
No
Our Verdict
The Asus RT-AX86S is an exceptional budget-friendly gaming router, perfect for those seeking a blend of performance and value. Its 5 GHz band delivers impressive download speeds of up to 563 Mbits/s, ensuring smooth and lag-free gaming sessions, a crucial aspect for serious gamers. The router also supports a broad coverage area of up to 140 feet, making it ideal for larger homes or spaces where stable connectivity is essential.
In addition to its speed and range, the Asus RT-AX86S offers advanced features like Quality of Service (QoS) prioritization, MU-MIMO support, and compatibility with management apps, providing users with a customizable and efficient networking experience. This router is not just limited to gaming; it’s also a strong contender for streaming, with its 5 GHz band supporting high-quality video streaming without buffering issues.
While it may not match the higher-end routers like the Netgear Nighthawk RAXE500 in terms of 6 GHz speeds and broader range, the Asus RT-AX86S still stands out for its reliability and performance in key areas. Its robust 5 GHz speed and extensive coverage make it a versatile option for various use cases, including streaming, gaming, and general home or small business internet needs.
For those on a budget, the Asus RT-AX86S offers an impressive balance of speed, range, and advanced features, making it a valuable addition to any home network setup. Whether you’re a gamer, streamer, or just need a reliable router for everyday use, this model provides excellent performance without breaking the bank.
Read Less

Best Overall

Runner Up

Best Value

Best Budget

Best Mid-Range

Premium Pick
Asus ROG GT6 Mesh
Best For Small Business
The Asus ROG GT6 Mesh router is ideal for gamers, content creators, and large homes, offering impressive speeds, extensive coverage, and seamless connectivity for bandwidth-intensive tasks.

True Score
81826Experts
864kCustomers
Absolutely Fresh
 $330.28
$330.28Read More
Snapshot
Reasons to Buy
- Fast Download/Upload Speed
- Easy to install and operate
Reasons to Avoid
- WiFi speed drops off at long range
- Connection range is limited
- Limited USB Connectivity
- Mediocre Latency
Specifications

# of LAN Ports 3 
Frequency Bands 2.4 GHz, 5.0 GHz 
MU-MIMO Support Yes 
Wireless Standard AC, AX, N 
Mesh System Yes 
Quality of Service Prioritization Yes 
# of Phone Ports n/a 
# of WAN Ports 1 
App Compatible Yes 
Available Storage 256MB 
Band Technology Tri 
Data Encryption Type WEP, WPA-Enterprise, WPA-PSK, WPA2-Enterprise, WPA3-Personal 
Energy Star Certified No 
Integrated Modem No 
LAN Port Speed 3 Gb Ethernet 
Number of Antennas 9 
Parental Controls Yes 
Processor Cores Triple 
Processor Speed 1.7GHz 
WiFi Range 5800 sq. ft 
WiFi Speed 2.6 Gb 
Wired Speed 2500 Mb All Specs
Test Results
2.4 GHz Download speed (Mbits/s) 139 5 GHz Download speed (Mbits/s) 701 6 Ghz Download speed (Mbits/s) 0 Latency (ms) 22 Router Range (ft) 95 2.4 GHz Upload speed (Mbits/s) 112 All Retailers
- $330.28
Availability
Free Shipping
- $349.99
Availability
Free Shipping
No
Our Verdict
The Asus ROG GT6 Mesh router is an excellent choice for gamers, content creators, and those with large homes who need seamless online connectivity. This router excels in both 2.4 GHz and 5 GHz bands, offering impressive speeds of 139.35 Mbits/s and 701.3 Mbits/s for downloads, and 111.9 Mbits/s and 618.5 Mbits/s for uploads, respectively. These speeds ensure smooth 4K streaming, online gaming, and efficient handling of multiple devices, making it ideal for bandwidth-intensive tasks.
One of the standout features of the GT6 Mesh is its extensive Wi-Fi coverage, reaching up to 95 feet. This ensures that every corner of your home is well-served, minimizing dead zones and providing a stable connection for all your devices. With a low latency of 22 ms, the router supports real-time gaming and high-quality video conferencing, offering a responsive and reliable online experience.
While the Asus RT-AX86S offers better range and lower latency at a more affordable price, the GT6 Mesh shines with its advanced mesh networking capabilities. This feature eliminates Wi-Fi dead zones and provides consistent coverage across large areas, making it the perfect solution for expansive homes and demanding online activities.
The Asus ROG GT6 Mesh router is a robust option for those needing extensive coverage, high-speed internet, and advanced features. Its superior upload speeds and mesh networking make it a valuable investment for competitive gamers, content creators, and professionals who require reliable, fast connectivity throughout large spaces.
Read Less

Did you know 49% of router reviewers are untrustworthy?
Our research found only 60 of 110+ router reviewers as of November 2025 can be trusted. This is why Gadget Review is committed to calculating the most accurate product scores on the web.
To do this, we give every router review site a Trust Rating, which measures how trustworthy the site and their testing claims are. We then leverage AI & a machine learning model to combine and calculate the Trust Rating with data from experts and consumers to deliver the True Score, the web’s most accurate product quality rating.
 191,622
191,622Router Reviews Analyzed

37
Total Products Analyzed

Best Overall

Runner Up

Best Value

Best Budget

Best Mid-Range

Premium Pick
Eero Max 7
Best For Mesh
The Eero Max 7 is a high-performance mesh router, perfect for bandwidth-intensive activities, offering exceptional 6 GHz speeds, low latency, and robust coverage for seamless streaming and gaming.

True Score
80807Experts
86908Customers
Absolutely Fresh
 SAVE $180$599.99$419.99
SAVE $180$599.99$419.99Read More
Snapshot
Reasons to Buy
- Exceptional Download WiFi Speed
- Easy Installation and Configuration
- Low Latency
Reasons to Avoid
- Poor 2.4 GHz Upload Speeds
- Short Range of Coverage
- Limited Port Space
Specifications

# of LAN Ports 4 
Frequency Bands 2.4 GHz, 5.0 GHz, 6.0 GHz 
MU-MIMO Support Yes 
Wireless Standard BE 
Mesh System Yes 
Quality of Service Prioritization No 
# of Phone Ports n/a 
# of WAN Ports 1 
App Compatible Yes 
Available Storage 4000MB 
Band Technology Tri 
Data Encryption Type WPA2-Personal, WPA3-Personal 
Energy Star Certified No 
Integrated Modem No 
LAN Port Speed 2 Gb Ethernet 
Number of Antennas 10 
Parental Controls Yes 
Processor Cores Quad 
Processor Speed – 
WiFi Range 2500 sq.ft 
WiFi Speed 4.3 Gb 
Wired Speed 10000 Mb All Specs
Test Results
2.4 GHz Download speed (Mbits/s) 96 5 GHz Download speed (Mbits/s) 1,078 6 Ghz Download speed (Mbits/s) 1,223 Latency (ms) 7 Router Range (ft) 90 2.4 GHz Upload speed (Mbits/s) 75 All Retailers
- $419.99$600Save $180
Availability
In StockFree Shipping
Yes - $419.99$600Save $180
Availability
In StockFree Shipping
No - $419.99$600Save $180
Availability
Free Shipping
Our Verdict
The Eero Max 7 is a standout choice for those seeking a high-performance mesh network solution, especially for bandwidth-intensive activities. With its exceptional 6 GHz band capabilities, this router offers a best-in-class download speed of 1222.5 Mbits/s and an upload speed of 638 Mbits/s, making it perfect for 4K video streaming, lag-free online gaming, and smooth video conferencing. It’s an ideal option for tech enthusiasts, streamers, and competitive gamers who demand the fastest wireless speeds for their digital lifestyle.
Additionally, the Eero Max 7 features tri-band technology, providing impressive speeds on the 5 GHz band with a download speed of 1078.5 Mbits/s and an upload speed of 410.6 Mbits/s. This ensures robust connectivity for various tasks without interference. The 2.4 GHz band also delivers reliable speeds, with 95.9 Mbits/s for downloads and 74.8 Mbits/s for uploads, suitable for everyday internet use.
With a low latency of just 7 ms, the Eero Max 7 ensures quick response times, crucial for seamless gaming and video calls. Its coverage range extends to 90 ft, making it suitable for small to medium-sized homes. Compared to other routers like the Netgear Nighthawk RAXE300, the Eero Max 7 stands out with its superior 6 GHz speed, making it the go-to choice for high-definition streaming, VR applications, and multiple demanding devices.
Despite its premium price, the Eero Max 7’s top-tier performance and comprehensive mesh networking capabilities justify the investment, offering an unparalleled high-speed online experience across all your devices.
Read Less

DON’T SEE WHAT YOU’RE LOOKING FOR?
If you’re looking for a router that fits specific needs, consider exploring the best Wi-Fi routers for long-range, perfect for larger homes or offices. If security is a top priority, our guide on the best secure routers might be exactly what you need.
For those who require VPN integration, the best VPN routers provide excellent options for maintaining privacy. On the other hand, if you’re working with a fiber-optic connection, our recommendations for the best fiber-optic routers are tailored for high-speed internet. For a more traditional setup, check out the best wired routers that offer reliable performance without wireless interference.
Small business owners may find our list of the best small business routers invaluable. Travelers aren’t left out either – the best travel routers ensure you stay connected on the go. Additionally, if you’re using specific ISPs, our guides for the best routers for Fios, Google Fiber, Spectrum, or Xfinity can help you find the perfect match.
Lastly, brand enthusiasts might prefer checking out the best Netgear routers, Asus routers, or TP-Link routers to ensure you’re getting a device that meets your expectations.

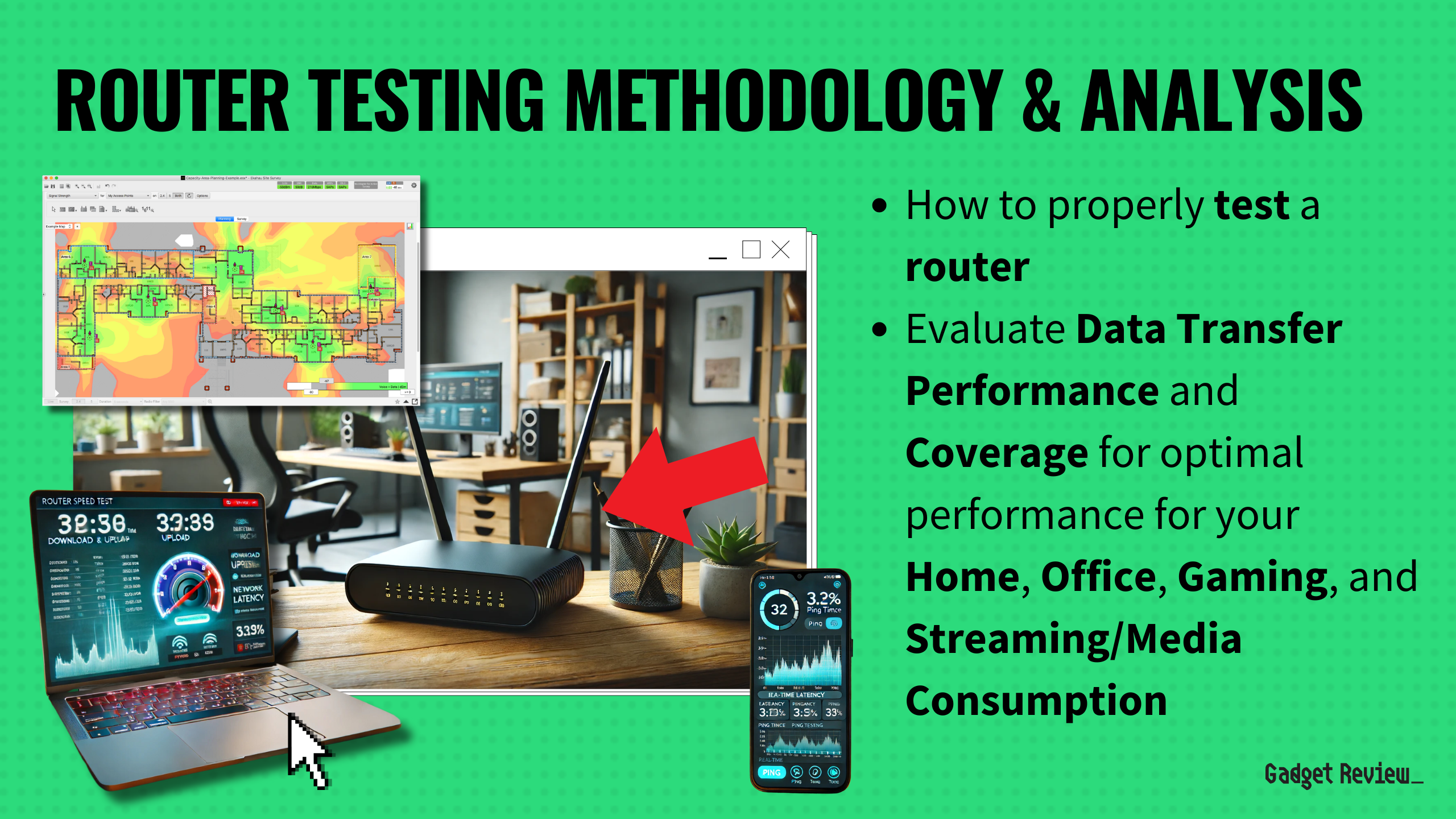
Our Approach to Evaluating Routers
We’ve redefined router buying guides, setting us apart from any other site on the planet. Our unique approach uses a comprehensive dataset from trusted sites, focusing on key testing metrics like download speeds across multiple bands, upload speeds along those same bands, latency, and range.
We aggregate and analyze this data, ensuring our recommendations meet the specific needs. Specifically, when it comes to routers, this involves selecting models that deliver good range, good speeds, and low latency. Discover our data-driven methodology for precise, reliable router recommendations.
Which Criteria Matters for Testing Routers?
By focusing on these criteria, anyone can quickly and easily compare these routers and how they’ll perform. This helps you make an informed decision and purchase a router that will perform excellently in just about any situation.
| CRITERIA | RANGE | REQUIRED | DEFINITION |
|---|---|---|---|
| 2.4 GHz Download Speed | > 50 Mbits/s | Yes | The maximum speed that the router can reach when downloading on the 2.4 GHz band. |
| 2.4 GHz Upload Speed | > 25 Mbits/s | No (Nice to have) | The maximum speed that the router can reach when uploading on the 2.4 GHz band. |
| 5 GHz Download Speed | > 200 Mbits/s | Yes | The maximum speed that the router can reach when downloading on the 5 GHz band. |
| 5 GHz Upload Speed | > 100 Mbits/s | No (Nice to have) | The maximum speed that the router can reach when uploading on the 5 Ghz band. |
| 6 GHz Download Speed | > 250 Mbits/s | No (Nice to have) | The maximum speed that the router can reach when downloading on the 6 Ghz band. |
| 6 GHz Upload Speed | > 125 Mbits/s | No (Nice to have) | The maximum speed that the router can reach when uploading on the 6 Ghz band. |
| Router Range | > 50 ft | No (Nice to have) | How far a device can be from a router before the signal starts degrading. It is worth noting that 2.4 GHz reaches further than 5 GHz. |
| Latency | < 40 ms | No (Nice to have) | The delay that is created by a signal being sent by the router and then received. |
Our Trusted Data Sources
We looked at 110+ router reviewers and found that 60 are trustworthy (60%+ Trust Rating). The three we have listed below are our most trusted for routers.
- Daniel Cooper – Engadget
- Joel Santo Domingo – Wirecutter, MuckRack
- James Morris – Kit Guru, LinkedIn
Interested in a comprehensive analysis of our data sources? We’ve got you covered. Below, you’ll find a detailed list of every router review website we’ve identified, organized by their respective Trust Ratings from highest to lowest. But we didn’t stop there. We’ve meticulously reviewed each publication and verified the data by checking whether the authors have bio links to MuckRack or LinkedIn. We’re committed to not only checking the facts but ensuring their veracity.
Router Test Data & Results
Disclaimer:
Evaluating router performance is more than hardware analysis. While hardware tests are straightforward, the challenge lies in contextualizing the results within the limits of real-world usage. Routers operate under conditions that testers cannot fully standardize, including variations in Internet Service Providers (ISPs), network traffic congestion, discrepancies between advertised and actual Internet speeds, and the physical layout of homes. These factors introduce a degree of unpredictability, making it hard to draw universal conclusions. As such, our router recommendations aim to provide useful general guidance, accommodating a wide range of home environments and internet setups.
1. 2.4 GHz Download Speed (Mbits/s)
The oldest and slowest of the bands on a router is the 2.4 GHz band, but it sticks around for a reason. Generally speaking, while this band features the slowest available speeds and has the lowest bandwidth, but also reaches out the furthest. It’s not the best band to connect to connect if you need high speeds, but if you just need to be connected for light browsing or anything that’s low bandwidth, it works. Alternatively, if you own a lot of old devices, this band may be the only band they can “see” and therefore, use.
Given the age of the band, top speeds on 2.4 GHz cap out very quickly. We recommend a speed of at least 50 Mbits/s, but if you aren’t really going to be using this band for anything other than checking web pages, you can go lower. It’s worth noting, though, that this might lead to a more frustrating and laggier time on modern sites with lots of scripting and high-quality images.
2.4 GHz Download Speed
> 50 Mbits/s
Acceptable range of performance
Definition: The top speed the router reaches downloading on the 2.4 GHz band.
Units of Measurement: Mbits/s (megabits per second)
Tools to Measure: Speed-checking software
Why It’s Important:
For older devices or for connecting at a longer range, the 2.4 GHz frequency is the only one that you’ll be able to use, so it should have usable speed.
2.4 GHz Download Speed (Mbits/s; higher is better; 0 = No Data)
2. 2.4 GHz Upload Speed (Mbits/s)
2.4 GHz Upload Speed
> 25 Mbits/s
Acceptable range of performance
Definition: The top speed the router reaches uploading on the 2.4 GHz band.
Units of Measurement: Mbits/s (megabits per second)
Tools to Measure: Speed-checking software
Why It’s Important:
For older devices or for connecting at a longer range, the 2.4 GHz frequency is the only one that you’ll be able to use, so it should have usable speed.
Upload speed is just the reverse of download speed. Instead of pulling down info, you’re uploading it. This is common when uploading documents or photos to a website or when you’re streaming content to a platform like Twitch.
Generally speaking, your upload speed is going to be limited more by your ISP than by your router, because bandwidth is a two-way street when it comes to routers. Pulling 100 MBits down means you should be able to push 100 MBits up, but if your ISP throttles your upload, then it doesn’t matter if your router allows for a full gigabit up, you can only go as fast as the “speed” limit allows. It’s for that reason we set 2.4 GHz upload limits at 25 Mbits, but in reality, anything you can get is acceptable, since this band isn’t – and shouldn’t – be used for anything that requires real speed.
2.4 GHz Upload Speed (Mbits/s; higher is better; 0 = No Data)
3. 5 GHz Download Speed (Mbits/s)
The much faster 5 GHz band offers up much greater bandwidth and is much, much better at meeting high-speed demands. Streaming high-quality video, using streaming services, gaming, downloading large files and games – the 5 GHz band is what makes all of these activities quick and bearable. It reaches a lower range than the 2.4 GHz band, but it’s also much faster, so you’ll use it more, especially on newer devices that actually support the band.
Given how much you’ll be using this band, we recommend a speed of at least 200 Mbits/s to ensure you’re able to enjoy streaming and gaming on at least a few devices simultaneously. Any lower and you start to run into real bottleneck concerns, such as endless buffering, lagging, or drops in connection.
5 GHz Download Speed
> 200 Mbits/s
Acceptable range of performance
Definition: The top speed the router reaches downloading on the 5 GHz band.
Units of Measurement: Mbits/s (megabits per second)
Tools to Measure: Speed-checking software
Why It’s Important:
This band is used by most modern devices and offers greater speeds that enable activities like gaming and HD streaming on multiple devices.
5 GHz Download Speed (Mbits/s; higher is better; 0 = No Data)
4. 5 GHz Upload Speed (Mbits/s)
5 GHz Upload Speed
> 100 MBits/s
Acceptable range of performance
Definition: The top speed the router reaches uploading on the 5 GHz band.
Units of Measurement: Mbits/s (megabits per second)
Tools to Measure: Speed-checking software
Why It’s Important:
This band is used by most modern devices and offers greater speeds that enable streaming in higher quality to places like Twitch.
Just as 5 GHz download speed is faster than 2.4 GHz download, 5 GHz upload is usually faster than 2.4 GHz download. Why “usually”? Because if your upload cap is extremely aggressive, you might not notice a difference. This is purely ISP-dependent, but it’s worth keeping in mind that seeing an unusually low 5 GHz upload isn’t necessarily a router issue, and could just be your ISP throttling your connection. It’s worth noting that, despite the naming convention, 5 GHz is what’s used by Wi-Fi 6 (and also Wi-Fi 5) routers.
We recommend a speed of at least 100 Mbits/s, but you’ll want more if you plan on doing any kind of streaming to a platform like YouTube or Twitch and want to stream at a decent quality. Unfortunately, your choice of router isn’t the only thing that will determine the speed you get out of your connection – if your connection throttles you to 80 Mbits up, then nothing you buy will fix that.
5 GHz Upload Speed (Mbits/s; higher is better; 0 = No Data)
5. 6 GHz Download Speed (Mbits/s)
The 6 GHz band is the latest band available on routers and is exclusive to routers that use Wi-Fi 6E. It’s slightly faster than 5 GHz bands, but the primary draw behind using 6 GHz is the reduced congestion, which reduces signal interference and as such, can potentially boost latency and speed. The newest devices can connect to Wi-Fi 6E, and because it’s a new standard, all new devices will eventually come to support it.
Because the band is only slightly faster than 5 GHz (if it ends up faster at all), we recommend a download speed of 250 Mbits/s. This is plenty for streaming, playing games, and watching Netflix – or all three across several devices, without seeing lag spikes or buffering. If you have new devices that support Wi-Fi 6E, you’ll need a router that supports the 6 GHz band to take advantage of it. Also, similar to how 5 GHz has a shorter range than 2.4 GHz, 6 GHz has a slightly shorter range than 5 GHz.
6 GHz Download Speed
> 250 Mbits/s
Acceptable range of performance
Definition: The top speed the router reaches downloading on the 6 GHz band.
Units of Measurement: Mbits/s
Tools to Measure: Speed-checking software
Why It’s Important:
If you’re connecting a ton of devices to a network, this band offers a high-speed low-congestion way to get them all high speeds on demand.
6 GHz Download Speed (Mbits/s; higher is better; 0 = No Data)
6. 6 GHz Upload Speed (Mbits/s)
6 GHz Upload Speed
> 125 Mbits/s
Acceptable range of performance
Definition: The top speed the router reaches uploading on the 6 GHz band.
Units of Measurement: N/A
Tools to Measure: Speed-checking software
Why It’s Important:
If you’re connecting a ton of devices to a network, this band offers a high-speed low-congestion way to get them all high speeds on demand.
Just as the 6 GHz band allows for low congestion connections that help reduce latency and improve download speed for multiple devices, it also can improve upload speed. You’re still limited by your ISP, but you run the lowest chance of hitting major spikes in lag or dropping your connection when connected to this band.
We recommend a speed of at least 125 Mbits, but higher is obviously going to be better. Still, you’re only going to go as high as your ISP ultimately allows, so if you see low speeds, it’s worth checking what your ISP throttles upload speeds to.
6 GHz Upload Speed (Mbits/slower is better; 0 = No Data)
7. Router Range (ft)
The router range is exactly what the name suggests: how far can you get from the router before you start experiencing issues with your connection? The complicating factor is the simple fact that the range depends on the band you’re using. 2.4 GHz is a band that offers greater range, so it gives test results that show a greater range than tests that use the 5 GHz band. In general, our research found most publications used the 5 GHz band, so our recommendations are based on that.
As such, we recommend your router have a range of at least 50 ft. This gives you a good “bubble” around the router that you can connect to, but it’s important to know that things like the walls in your home can cause issues. Thicker walls block more signal, thinner walls block less. Some materials will also do a better job than others will at stopping signal, so if you see a router with a range of 65 ft, know that it might not reach that far in your home. It could reach further – or not nearly as far. This is also why you get dead zones in your home – it’s a matter of geometry and materials.
Router Range
> 50 ft
Acceptable range of performance
Definition: The distance the router transmits reliable signal out to before performance and speed degrades.
Units of Measurement: Feet (ft)
Tools to Measure: Measuring Tape
Why It’s Important:
Range impacts how far you’ll get a reliable connection in your home, and whether you’ll need extenders or not.
Router Range (ft; higher is better; 0 = No Data)
8. Latency (ms)
Latency
< 40 ms
Acceptable range of performance
Definition: The time it takes for the router to send and then receive signals.
Units of Measurement: Milliseconds (ms)
Tools to Measure: Speed-checking software
Why It’s Important:
Latency is important to reduce delay when gaming and video conferencing.
On a router, latency refers to how long it takes for the router to send out and receive a signal. The longer it takes, the more delay there is between you sending and receiving data, which can introduce lag in video games and also makes video conferencing harder since the person you’re speaking with now has to contend with your delay and vice versa. If you’ve ever spent a call talking over someone because you don’t know they started talking a second ago, that’s latency.
For that reason, we recommend a latency below 40 ms. As low as you can get it is obviously preferable, but latency is another aspect of your internet connection that is hard to manage. Latency differs to every single place you connect to, and every ISP has its own latency they “add” because you have to connect to their service too. Latency creeps in from your ISP, from the site you’re requesting data from, from your router, and from your own onboard Wi-Fi antenna – and that’s just to name a few sources. If you’re gaming, you also have a delay introduced by your connection to game servers and the delay that exists on a hardware level when you input commands.
Latency (ms; lower is better; 0 = No Data)
Best Routers: Mistakes To Avoid
- Ignoring The Router’s Standard: Buying a router with an outdated standard can limit network speed, range, and device compatibility. It’s important to choose a router that supports at least Wi-Fi 5 (802.11ac), though Wi-Fi 6 or Wi-Fi 6E are preferable for future-proofing. For instance, understanding the different types of routers available and ensuring your router matches your modem are crucial steps in the selection process. Additionally, knowing how to replace your ISP router with your own can also make a significant difference in performance.
- Buy Enough Coverage: Underestimating the size of the area the Wi-Fi needs to cover can lead to dead zones while overestimating can mean spending more than necessary. Consider the size of your home, the layout, and any potential interference sources. Mesh Wi-Fi systems can be a good solution for larger homes or homes with thick walls that suffer from lots of dead zones. When comparing a Wi-Fi router vs. an extender, it’s crucial to recognize that while a top extender, whether it’s single or dual band, can help in smaller areas, a mesh system is often better for extensive coverage If you’re deciding between a mesh network and a traditional router, understanding the key differences is essential. Furthermore, if you find that your Wi-Fi signal keeps disconnecting, it might be due to these dead zones or interference sources, and knowing how to troubleshoot issues like your router turning off can save a lot of frustration.
- Chasing Top-Shelf Specs With Budget Internet: High-performance routers can be expensive, and the highest specs may not always be necessary, especially if you’re using a budget internet plan. Check your plan’s listed internet speed and buy to suit that. It’s also important to consider how many devices you plan on having connected and how intensively you use them. Knowing what router you have, and how to set up your router as a bridge can also be helpful if you’re looking to improve your network without investing in top-tier equipment. Be sure to understand the differences between bridge mode and router mode to get the most out of your setup. Additionally, selecting between a business router versus a home router depends on your specific needs and should align with your internet usage. Overpaying for features you don’t need can quickly become an unnecessary expense.
- Ignoring Wired Ports And Non-Wireless Connectivity: Consider how many wired devices (e.g., desktop computers, gaming consoles, smart TVs) you plan to connect. Ensuring the router has enough Ethernet ports is crucial, as is understanding how to disable access to the router from the internet for security purposes. Some routers also offer USB ports for connecting printers or storage devices directly to the network, which can add to the network’s functionality. It’s also important to know how to check data usage on your Wi-Fi router to manage your network more effectively. Finally, in the case of troubleshooting issues like a red light on your Wi-Fi router, knowing the proper steps to resolve this can ensure your network stays operational.
The Best Routers Tests Compared
Product |
True Score
|
2.4 GHz D/L Speed
|
5 Ghz D/L Speed
|
6 GHz D/L Speed
|
Range
|
Latency
| |
|---|---|---|---|---|---|---|---|
| 83 |
|
|
|
|
| $158.40 $220 $62 |
| 83 |
|
|
|
|
| $132.96 |
| 81 |
|
|
|
|
| $330.28 |
| 80 |
|
|
|
|
| $419.99 $600 $180 |