Building a gaming rig for the latest AAA titles? Your shiny new RTX 5090 cracks passwords faster than it renders explosions. Kaspersky’s latest research reveals that 60% of passwords protected by MD5 hashing fall in under an hour when facing consumer gaming hardware—a sobering reminder that your entertainment investment doubles as an unintentional cybersecurity weapon.
World Password Day Brings Grim Statistics
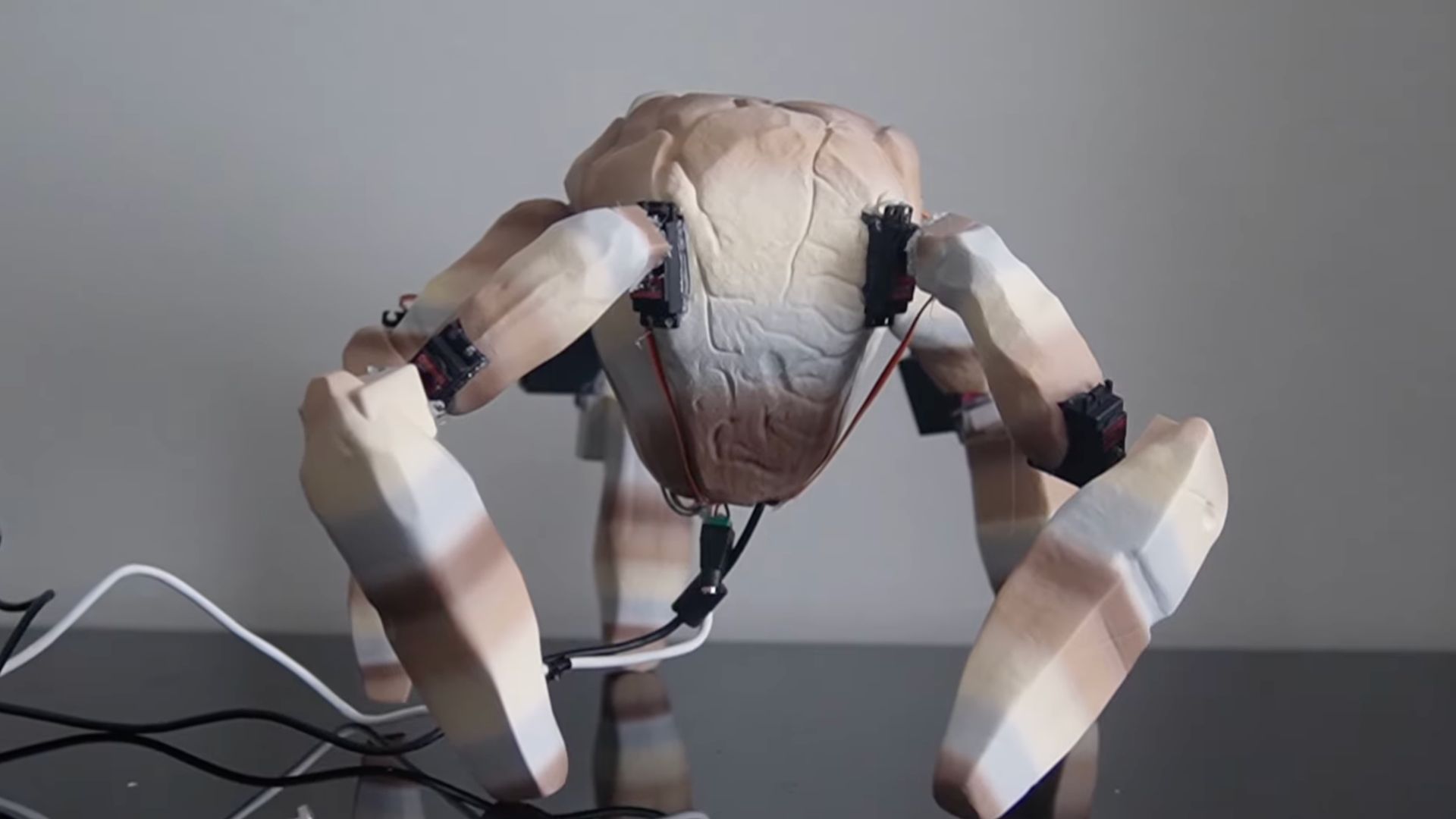
Gaming GPUs achieve billions of password guesses per second on vulnerable hash algorithms.
Kaspersky researchers analyzed 231 million leaked passwords this World Password Day, discovering that gaming GPUs demolish password security with embarrassing efficiency. The RTX 5090 achieves 219.5 billion guesses per second on MD5 hashes, while 48% of passwords surrender in under 60 seconds. This represents a slight uptick from 2024’s 59% hourly crack rate, driven entirely by advancing GPU architecture rather than improving password habits.
The performance gap between consumer and enterprise hardware tells a remarkable story. Your $2,000 gaming GPU outperforms $30,000 enterprise AI cards by 63% on average across various hashing algorithms. Previous-generation RTX 4090 cards already hit 82 billion guesses per second—fifteen times faster than top-tier CPUs.
MD5’s Fatal Flaw Meets Modern Hardware
The algorithm’s design for speed creates perfect conditions for GPU-accelerated attacks.
MD5’s vulnerability stems from its original design philosophy: speed over security. While salts protect against rainbow table attacks, they’re useless against brute-force attempts on leaked databases. Think of it like using a screen door as home security—adding a prettier frame doesn’t stop determined intruders.
Steven Furnell from the University of Nottingham puts it bluntly: “Passwords protected only by fast hashing algorithms such as MD5 are no longer safe.” Sites clinging to MD5 essentially hand criminal networks a master key when breaches occur.
Your Digital Defense Strategy Needs an Upgrade
Modern password protection requires deliberately slower hashing algorithms designed for security.
This research highlights why modern alternatives like bcrypt, Argon2, and passkeys exist. These technologies deliberately slow down processing, making GPU-accelerated attacks economically unfeasible. Meanwhile, your accounts on legacy sites remain vulnerable until administrators modernize their security infrastructure.
The irony cuts deep: gaming hardware designed for entertainment accidentally became cybersecurity’s biggest threat. Your weekend gaming session and a hacker’s password-cracking operation now use identical tools, just with different intentions.