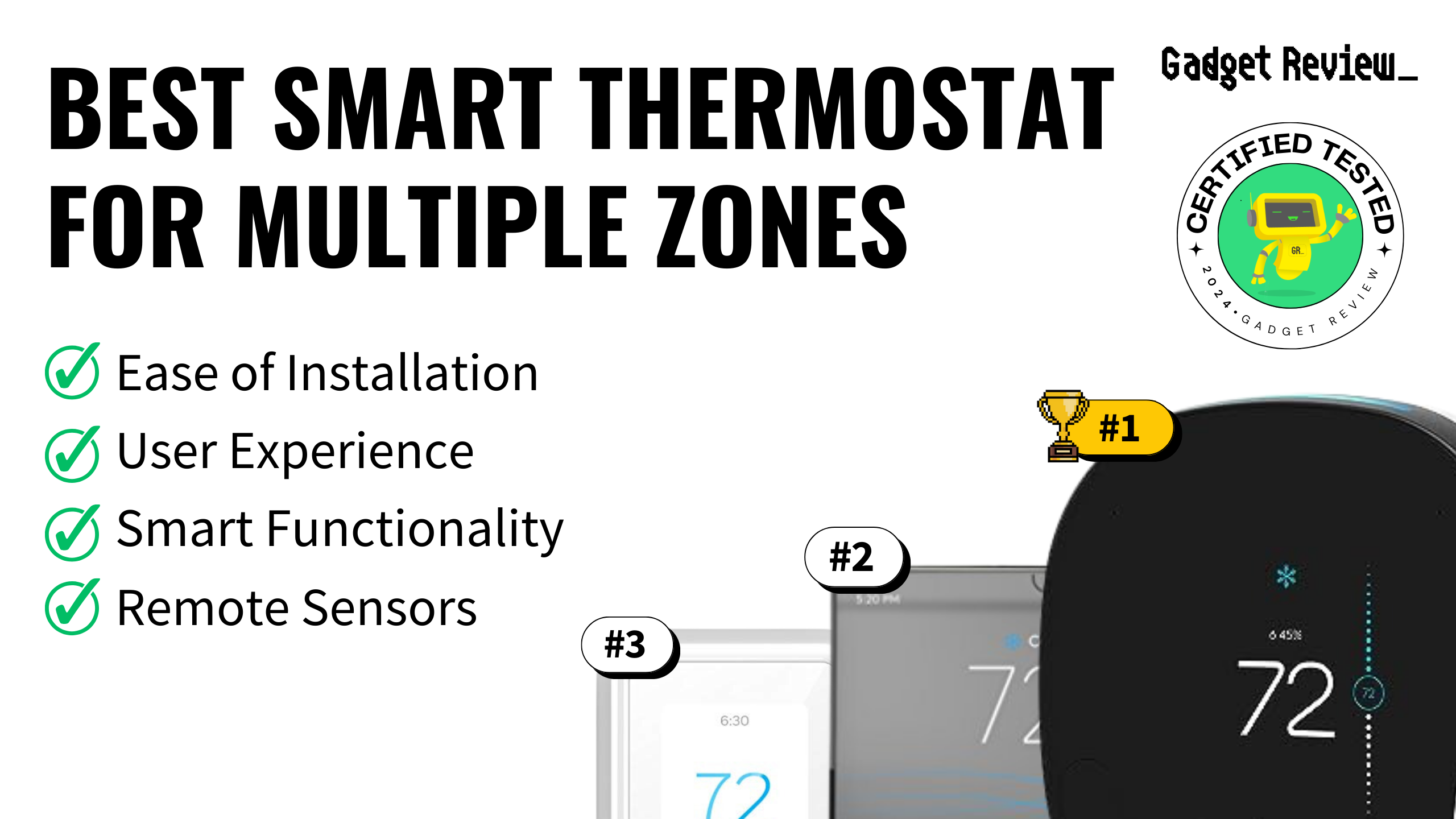
To help you find the best smart thermostat for multiple zones, we took the time to research all of the different options available today and analyze their features and customer reviews for you. During our research and analysis, we determined the top features to be smart home compatibility, remote sensor availability, and overall user-friendliness. We recommend purchasing a smart thermostat that’s easy to install and easy to use, regardless of where you are. Other features to consider include geofencing and voice command compatibility.
With all of these features and considerations in mind, we selected the Ecobee4 as the best smart thermostat for multiple zones. Keep reading below to learn more about this top pick and the other options we ranked.
Top 10 Best Smart Thermostat for Multiple Zones
#1 Ecobee4 Smart Thermostat for Multiple Zones
Award: TOP PICK
WHY WE LIKE IT: This top-of-the-line smart thermostat includes a remote sensor in your purchase, along with the ability to pair up to 32 total, so you can get accurate heating and cooling in any room of your house. It’s also designed incredibly well and even includes Amazon Alexa built directly into the thermostat itself.
- Sleek, compact design
- Integrated Amazon Alexa voice control
- Includes remote sensor
- Built-in speaker isn’t the loudest
- No geofencing capabilities
The Ecobee4 smart thermostat features a ton of expanded functionality over previous generations, bringing it fully into the age of capable, fully-connected smart homes. For starters, this is the first Ecobee thermostat to include Amazon Alexa voice control built directly into the device, including a speaker so you can hear Alexa’s responses from the thermostat. The speaker isn’t very loud, though, so you’ll need to listen closely or remain near the Ecobee to get the best experience. If you like controlling everything in your house with your voice, this is an excellent option for you.
The design of the Ecobee4 remains largely the same over previous versions, which is a good thing. It’s sleek and minimalist in its form factor. You can manually control everything on the Ecobee’s touchscreen, or you can make adjustments on the smartphone app. The Ecobee smart thermostat is also really easy to install, taking most people around 30 minutes on average. With the Ecobee, multiple zones functionality is made easy. Your purchase includes a single remote sensor so you can use the device for heating and cooling in multiple zones. Plus, you’ll have the ability to pair up to 32 individual sensors for larger spaces. The Ecobee4 also features geofencing functionality, which senses when you leave or return to your home and adjusts the temperature accordingly. This is a nice feature to have, but it only works for Android smartphone users.
#2 Glas Smart Thermostat for Multiple Zones
Award: HONORABLE MENTION
WHY WE LIKE IT: With the largest touchscreen display of any smart thermostat we’ve reviewed, this option brings a futuristic aesthetic and more user-friendliness to the table. You’ll also get advanced air quality detection functionality, so you can ensure your home’s air is always good.
- Huge, user-friendly display
- Tracks CO2, humidity, and VOC levels
- Includes remote sensor
- Doesn’t currently support remote sensors
- Setup is somewhat complicated
The Johnson Controls Glas smart thermostat offers one of the most unique designs we’ve seen to date. With a 5.5 x 3 inch touchscreen, you’re getting a ton of real estate and easier overall usability. When not active, the display is see-through, but as soon as you walk by, the motion sensors will wake the screen. Everything on the screen is displayed clearly and looks good in any lighting. Of course, with a larger display, you should expect the Glas thermostat to take up a lot of room on your wall, especially when compared to other smart thermostats.
When it comes to functionality and performance, you’ll find the Glas thermostat packed to the brim. Apart from the standard temperature controls, this smart thermostat also provides air quality monitoring, including detecting levels of CO2, humidity, and volatile organic compounds (VOC). If it senses a problem with any of these levels, the Glas will notify you and give you suggestions for how to fix the problem. The overall installation process was easy enough, but it’s definitely more complicated than other smart thermostats, especially if you haven’t installed one in the past. Unfortunately, the Glas doesn’t yet support remote sensors, so you’ll need a separate unit for each zone in your house that you want to control.
#3 Honeywell Home T9 Smart Thermostat for Multiple Zones
Award: BEST FOR REMOTE DETECTION
WHY WE LIKE IT: If you prefer to use remote sensors for heating and cooling multiple zones in your home, then this is the smart thermostat for you. Its remote sensors are incredibly accurate, versatile, and easy to install.
- Accurate remote temperature detection
- Easy installation
- Dual-band Wi-Fi for reliable connectivity
- No support for Apple HomeKit
- No motion sensor on main unit
The Honeywell Home T9 is the first Honeywell multi-zone thermostat to use remote sensors for more customized heating and cooling in your home. Fortunately, the T9 does this extremely well. It includes a single remote sensor in your purchase, with the option of pairing more as needed, up to 20 total. The sensors are powered by AAA batteries, mount to the wall, and offer incredibly accurate temperature readings. The remote sensors also offer an incredible range to stay connected to the main unit, which is a huge plus for big homes. With these sensors installed, the Honeywell T9 can tell when people are occupying rooms and automatically adjust your home’s temperature to meet predetermined settings.
Unfortunately, the main unit of the Honeywell T9 doesn’t feature any motion sensing to act the same way as a remote sensor, which was a little disappointing. Other than that, though, the design of the T9 smart thermostat is simple and unassuming. It looks good in virtually any home and features a bright touchscreen display that’s easy to use and read. The unit is compatible with Amazon Alexa and Google Assistant for voice control, but not with Apple HomeKit, which is a glaring omission. We’re hoping for a future update to include HomeKit compatibility, but we’re not holding our breath. Another great feature here is the dual-band Wi-Fi connectivity. This means you’ll get a more reliable wireless connection for the Honeywell T9, so you won’t have to worry about not being able to adjust your temperature via the mobile app.
#4 Ecobee SmartThermostat with Voice Control Smart Thermostat for Multiple Zones
Award: BEST USER FRIENDLY
WHY WE LIKE IT: This new and improved smart thermostat improves upon nearly everything from previous generations, including a much higher quality speaker, fully integrated Alexa support, and more accurate remote sensors. Plus, it’s incredibly easy to use and install for the best user experience.
- Improved speaker quality over last gen
- Fully Alexa capable
- Includes accurate remote sensors
- Larger than comparable models
- Display features a large bezel
The Ecobee SmartThermostat with Voice Control is the 5th generation smart thermostat from the ever-popular smart home brand. Since it’s the latest product in their lineup, you can expect a lot out of the Ecobee SmartThermostat. It’s fully integrated with Amazon Alexa and can act as a standalone Alexa speaker. Fortunately, the built-in speaker is much improved and can even play music from Spotify, and it sounds good while it does. Of course, the Ecobee is also compatible with Apple HomeKit and Google Assistant, if you prefer those voice assistants more.
This Ecobee smart thermostat also features an improved remote sensor. You’ll get one included with your purchase, and you’ll still have the ability to add up to 32 total sensors. The range is much improved on these sensors, so they’ll work even in the farther reaches of your home. We were also impressed with the addition of dual-band Wi-Fi compatibility here, which allows you to connect to either 2.4GHz or 5GHz Wi-Fi signals for a more reliable connection. Like previous generations, the Ecobee SmartThermostat is incredibly easy to use, both with its smartphone app and with the built-in touchscreen display. The only thing we would change here would be the extra-large bezel surrounding the display on the unit itself. If we could, we’d shrink it just a little so the thermostat wasn’t so large.
#5 Google Nest Learning Smart Thermostat for Multiple Zones
Award: BEST QUALITY
WHY WE LIKE IT: With intelligent learning capabilities, extensive compatibility with smart home devices, and a durable stainless steel design, this smart thermostat values quality over anything else. If you want the best-made thermostat without sacrificing functionality, you can’t go wrong here.
- Compatible with most home systems
- Durable stainless steel design
- New support for temperature sensors
- Not compatible with Apple HomeKit
The third generation of the Nest Learning smart thermostat is upon us, and it has brought more refinement and improvements with it. As with previous generations, this Nest thermostat offers intelligent internal components that start learning your habits as soon as the unit is installed. With an innovative combination of machine learning and temperature sensors, the Nest will create schedules for you and can even sense when there’s no one home, which will then indicate to the thermostat that it needs to go into energy-saving mode.
The Google Nest Learning smart thermostat is also designed incredibly well with a stainless steel body and high-resolution display. It’s incredibly easy to use and offers some of the most extensive compatibility with smart home systems. The only compatibility this thermostat lacks is with Apple’s HomeKit system. With this third-generation Nest thermostat, multiple zone control is made possible for the first time. It now supports remote sensors in multiple rooms so you can get a more accurate temperature throughout your entire home.
#6 Honeywell Lyric T5 Smart Thermostat for Multiple Zones
Award: BEST FOR VOICE CONTROL
WHY WE LIKE IT: This smart thermostat for multiple zones is one of the more options available today, but it doesn’t hold back in form or function. This thermostat is great for anyone who wants to control their HVAC system with their voice, due to its seamless voice control function with both Siri and Alexa systems.
- Supports geofencing capabilities
- Works seamlessly with Siri and Alexa
- Quick, easy installation
- No support for IFTTT
- No motion sensors
The Honeywell Lyric T5 smart thermostat may not look as sleek or as futuristic as the other smart thermostats available on the market today, but it is still an excellent choice because of its overall performance and capabilities. For starters, the Lyric T5 offers some of the best geofencing functionality of any of the products we reviewed in this buying guide. When properly configured, the Lyric’s geofencing function allows you to set an invisible radius around your home. Then, whenever you enter or exit that radius, the thermostat will run a pre-programmed schedule or power down into energy-saving mode, respectively.
Normal functionality is excellent here, as well, although the Lyric T5 does lack some of the more advanced features you can find today. For example, the thermostat doesn’t feature humidity sensors or motion sensing to know when you’re in the room. However, the thermostat is easy to use and easy to install. The best feature, though, is its voice control. The Honeywell supports voice commands with both Siri and Alexa, and the device recognizes your voice with minimal issues. Keep in mind that the Honeywell Lyric T5 doesn’t support remote sensor capabilities, so if you want to set up multiple zone performance, you’ll need to purchase more than one unit. Fortunately, the Lyric T5’s lower price point makes this much easier to accomplish.
#7 Emerson Sensi Touch Smart Thermostat for Multiple Zones
Award: BEST EASY INSTALLATION
WHY WE LIKE IT: With app-guided installation instructions, you can be sure to get the most user-friendly experience possible on this smart thermostat for multiple zones. This unit also features a responsive display and helpful back-glow lighting that keeps the area around the device lit in the dark.
- Easy, app-guided installation
- Extra-responsive touchscreen display
- Back-glow lighting keeps things illuminated
- Doesn’t create usage reports
- C-wire required
The Emerson Sensi Touch is an incredibly user-friendly smart thermostat that focuses on a streamlined design, extra-responsive display, and well-built smartphone app. However, most importantly, the Sensi Touch is incredibly easy to install because of its app-guided installation instructions. This free feature walks you through every single step of the installation process to make it simple for you, even if you have no experience. The only downside to the installation process is the fact that a C-wire is required. So if you don’t have one, you’ll likely want to consider a different thermostat unless you want to get a C-wire installed.
The Emerson thermostat is also really easy to use overall. The display is responsive, bright, and colorful, which makes manual adjustments easy. The mobile app is designed well, too, so all of your remote adjustments are easy. One of the best design features found here is the thermostat’s back-glow lighting. This keeps the immediate area around the thermostat lit for easier navigation and operation in the dark. Unfortunately, the Emerson Sensi Touch doesn’t generate usage reports for you, as other units do.
#8 Google Nest Thermostat E Smart Thermostat for Multiple Zones
Award: BEST SIMPLE DESIGN
WHY WE LIKE IT: This smart thermostat features all of the intelligent learning technology and features as its more premium siblings but at a much more affordable entry point. It also features a comprehensive smartphone app with generous reports and alert options.
- Excellent related app design
- Comprehensive reports and alerts
- Seamless pairing with other Nest devices
- Low-resolution display
- Flimsier plastic body
The Google Nest Thermostat E is the best option for you if you want all of the intelligent capabilities that the Nest line offers but don’t want to pay the premium price. Fortunately, the Nest Thermostat E can do everything the standard Nest Learning Thermostats can do, including learning your habits to automatically create heating and cooling schedules. It can also pair with smart home systems and works via voice commands on Alexa and Google Home systems.
We were also impressed by the Google Nest Thermostat E’s overall design. It’s not as durable as the premium versions of the device because of its plastic body, but it’s still streamlined and compact. This makes it perfect for people who like simple, minimalist designs. The Nest’s simple design also lends itself well to user-friendliness and easy installation, which a big bonus points. The Google Nest Thermostat E can also pair seamlessly with other Nest devices for a whole-home solution.
#9 Mysa Smart Thermostat for Multiple Zones
Award: BEST FOR HIGH VOLTAGE SYSTEMS
WHY WE LIKE IT: If you need a smart thermostat for controlling your high-voltage electric heating system, then this is the best option for you. This unit also features plenty of advanced features like humidity detection, automatic eco-mode, and smart home compatibility across the major brands.
- Sleek, minimal design
- Displays humidity levels
- Automatic eco mode saves on power
- No geofencing function
- Can’t control much manually
The Mysa smart thermostat is made specifically for electric heating systems and performs extremely well in those situations. Whether you have a high-voltage baseboard heater, radiant ceiling heating, or short- or long-cycle convectors, this is the best smart thermostat for you. It can handle heating systems up to a total of 3,800 watts of power. The Mysa is also compatible with most major smart home brands, including Google, Amazon, and Apple.
When it comes to performance and design quality, you won’t be disappointed by the Mysa smart thermostat. It offers one of the unique designs available, with a minimalist aesthetic and dot display. Unfortunately, this minimalist design means you won’t be able to control much manually from buttons on the thermostat. However, the smartphone app is designed really well, so you shouldn’t have any problems with overall usability. We were also impressed to find that the Mysa can display humidity levels for additional insight into your home’s air quality.
#10 iDevices IDEV0005AND5 Smart Thermostat for Multiple Zones
Award: BEST ON A BUDGET
WHY WE LIKE IT: If you’re on a budget, you absolutely cannot go wrong with this simple, streamlined, and effective smart thermostat. With a user-friendly mobile app and responsive voice controls with the major three voice assistant brands, this thermostat will get you up and running without much investment.
- Easy-to-use smartphone app
- Doesn’t require smart home hub
- Responsive voice controls
- Outdated design
- No touchscreen
There’s not a lot that’s special about the iDevices IDEV0005AND5 smart thermostat, but the ultra-low price makes it a worthy contender in an industry full of expensive hardware. If you want general smart home functionality for your HVAC system, but you don’t want to pay the price for it, then this is the perfect option for you. With this option, you’ll get the ability to control your heating and cooling schedules remotely directly from the palm of your hand with iDevice’s handy smartphone app.
The thermostat’s design is a little outdated, and it lacks a touchscreen, but it’s durable and easy to install. Even more impressive is the fact that you won’t require a smart home hub to get the thermostat to work. The iDevice IDEV005AND5 also gives you access to voice commands with Google, Amazon Alexa, and Apple HomeKit. All in all, if you want a budget smart thermostat for multiple zones, then this is the best choice for you.
How We Decided
As we started to research the best smart thermostats for multiple zones, we first considered each device’s ability to perform as desired. Of course, we only included smart thermostats above if they were capable of working to heat and cool individual portions of your home, independent from one another. However, we awarded bonus points for thermostats that can work with remote sensors so you don’t have to manually adjust the temperature for each thermostat.
Next, we looked at user-friendliness and ease of installation. We preferred smart thermostats that provided streamlined and simplified user interfaces, both on the thermostat itself and on the companion smartphone app. There will always be a learning curve when you first start using a smart thermostat, but we awarded bonus points to options that did everything possible to lessen the curve for first-time users. We also ranked options higher if they were easy to install in your home. You shouldn’t need to be an HVAC expert or electrician to install a new smart thermostat in your home. Most smart thermostats require a C wire for power, but we ranked options higher if they could still use alternative wiring setups for installation.
Finally, we considered the overall design and aesthetics. Since you’re possibly going to be installing multiple thermostats in a home, you’ll want something sleek and unobtrusive. We preferred thermostats with slim profiles with bright touchscreen displays. We also preferred models with smaller footprints so they weren’t taking up as much wall space overall.
Best Smart Thermostat for Multiple Zones Buyer’s Guide
The Most Important Features to Consider
- Ease of Installation
Installing a new thermostat is not something the average homeowner usually does. Fortunately, the overall installation process for smart thermostats is fairly easy. However, there are still a couple of things to consider when it comes to installing a new smart thermostat for multiple zones in your home. We recommend purchasing a thermostat that connects to your HVAC system’s power via a Common Wire, which is also known as a C wire. Most modern HVAC systems have a C wire. There are also systems that feature four-wire setups. Regardless of what kind of wire the heating and cooling system offers, your smart thermostat should have easy-to-follow installation instructions included in your purchase. - User Experience
By nature, smart thermostats for multiple zones are usually much easier to operate than non-smart alternatives. However, some offer even more simplified user interfaces and smartphone apps than competitors. Find a smart thermostat that is easy for you to use and understand, especially when it comes to more complicated processes like creating schedules. - Smart Functionality
Not all smart thermostats are made equal. Some offer more smart functionality than others. Look at what kind of smart features are most important to you, and purchase a thermostat that can do those things. For example, many smart thermostats can integrate with your home voice assistant system, like Google Assistant or Amazon Alexa. If controlling your home’s temperature with your voice is important to you for the ultimate smart home experience, you’ll want to purchase a model that can integrate with those systems. - Remote Sensors
In order to control multiple thermostats remotely in your house, you’ll need either multiple smart thermostats or a single device paired with remote sensors. These remote sensors detect the temperature and presence of people where they’re installed so that they can automatically tell the thermostat to heat up or cool down the room based on your pre-selected preferences. Not all smart thermostats are compatible with remote sensors, so if having automatic temperature adjustment is important to you, you’ll want to be sure the model you purchase works with remote sensors.